YNAK 16 in 1 Air Quality Monitor
YNAK 16 in 1 Air Quality Monitor
I was looking for something cheap to monitor air in my basement. I came upon this idea after building an arcade cabinet with MDF, and I thought to myself, “isn’t MDF toxic in some form?”. We won’t go into that. And my air is clean. But I did end up purchasing the YNAK 16 in 1 Air Quality Monitor. You can get it with a larger batter or in black vs. white, too.
The packing is fine and straightforward - actually probably better than I’d expect.

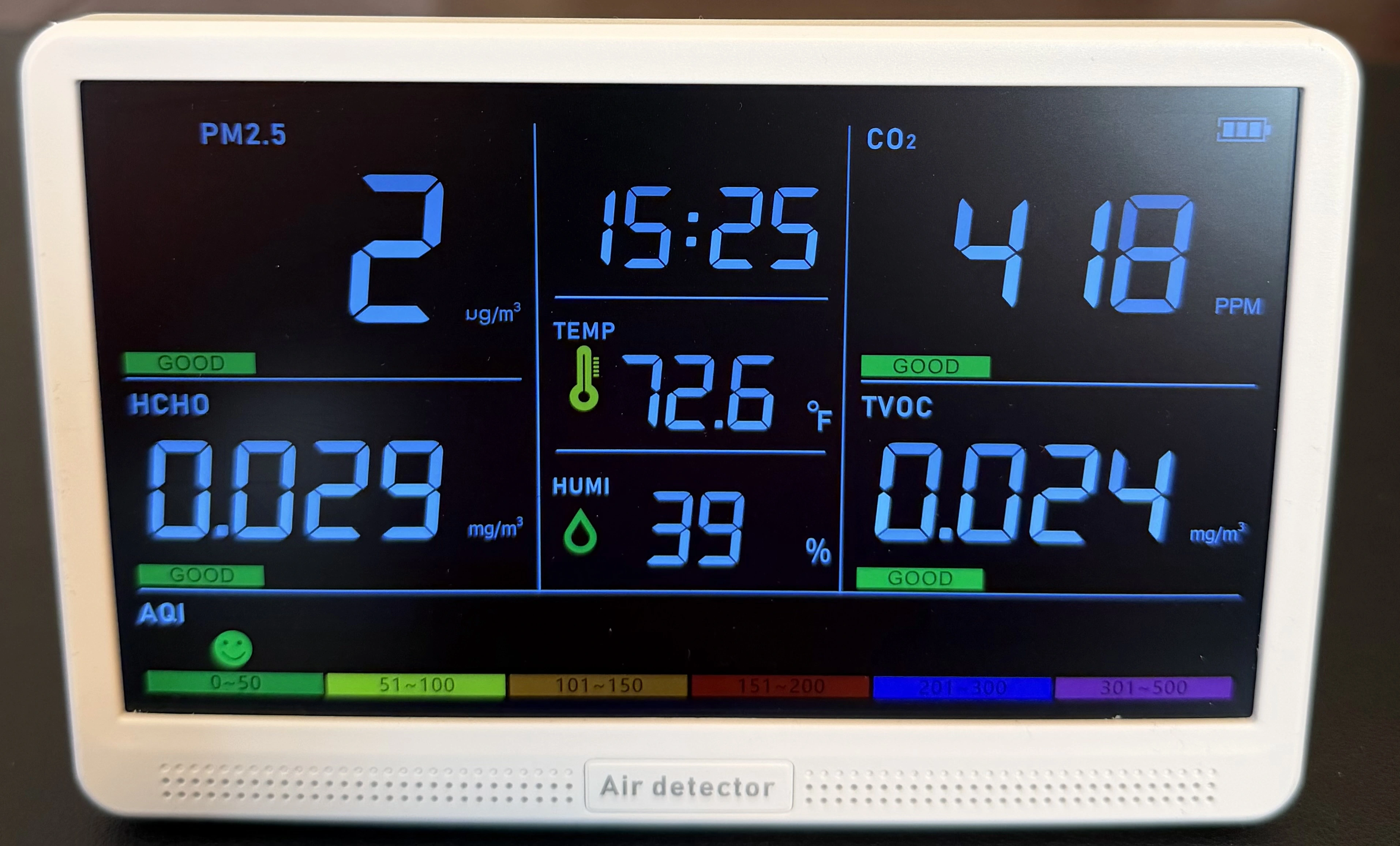
And honestly, the screen is pretty good for the price. It has several different brightness adjustments.
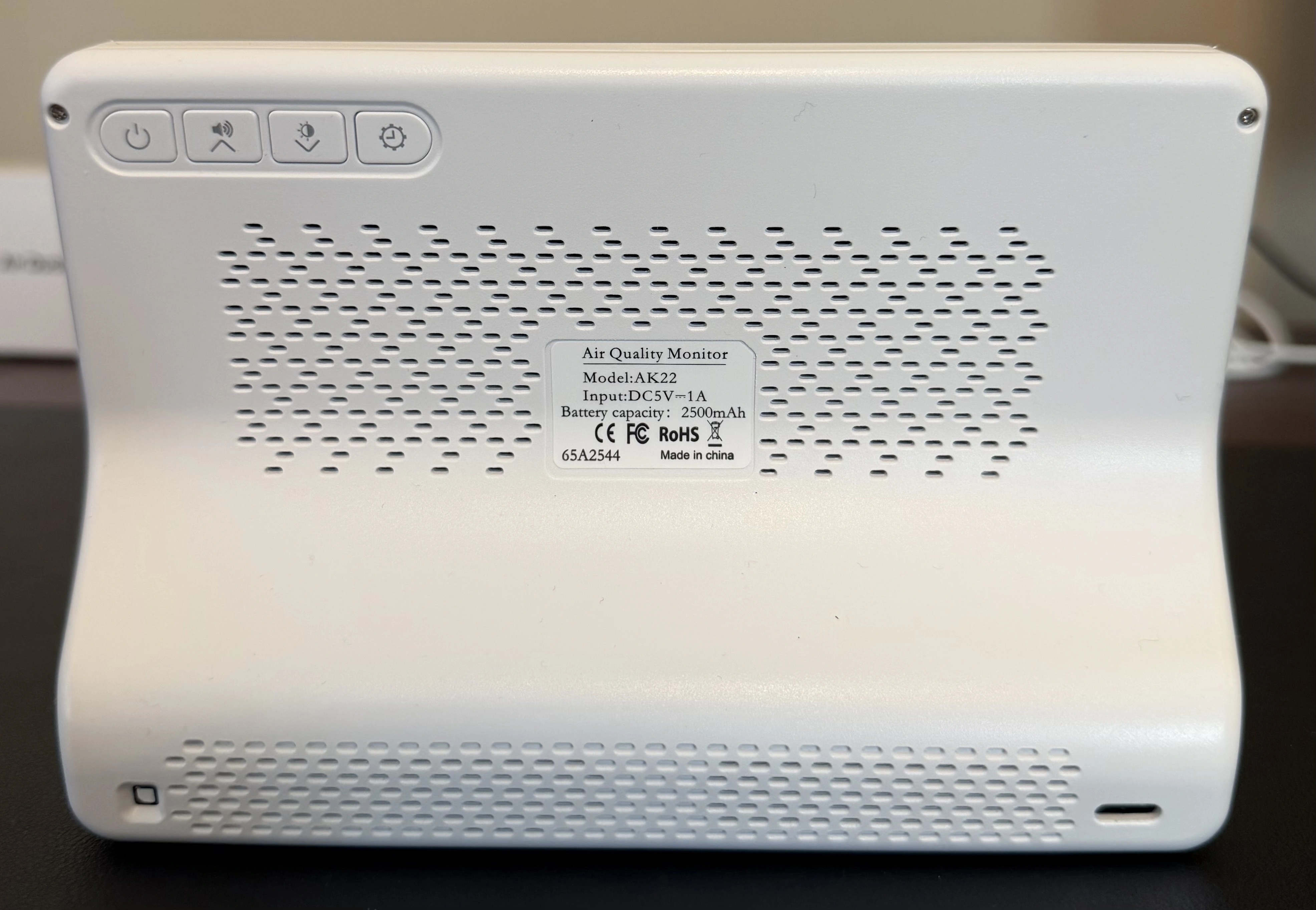
We see essentially a barebones back with a USB-C connection for power. Inside, we see the battery, which would be an easy upgrade to something larger (or maybe multiple batteries?).
Operation
Operation is dead simple. Plug it in. Press buttons on the back for brightness and noise. It is simple, functional, and effective. It seems to jive with other sensors I have around, too. So I’m not questioning accuracy, at this point.
We get readings for:
- Time
- PM1.0
- PM2.5
- PM10
- CO2 (likely estimated/eCO2)
- TVOC
- HCHO (formaldehyde)
- Temperature
- Humidity
- AQI (calculated)
YNAK 16 in 1 Air Quality Monitor Security
This thing does not have any connectivity — no WiFi, no Bluetooth, no Ethernet — so remote exploitation is effectively off the table. There’s no network stack, no radio, and no obvious way to interact with it unless you have physical access.
That said, once you open it up, things get more interesting.
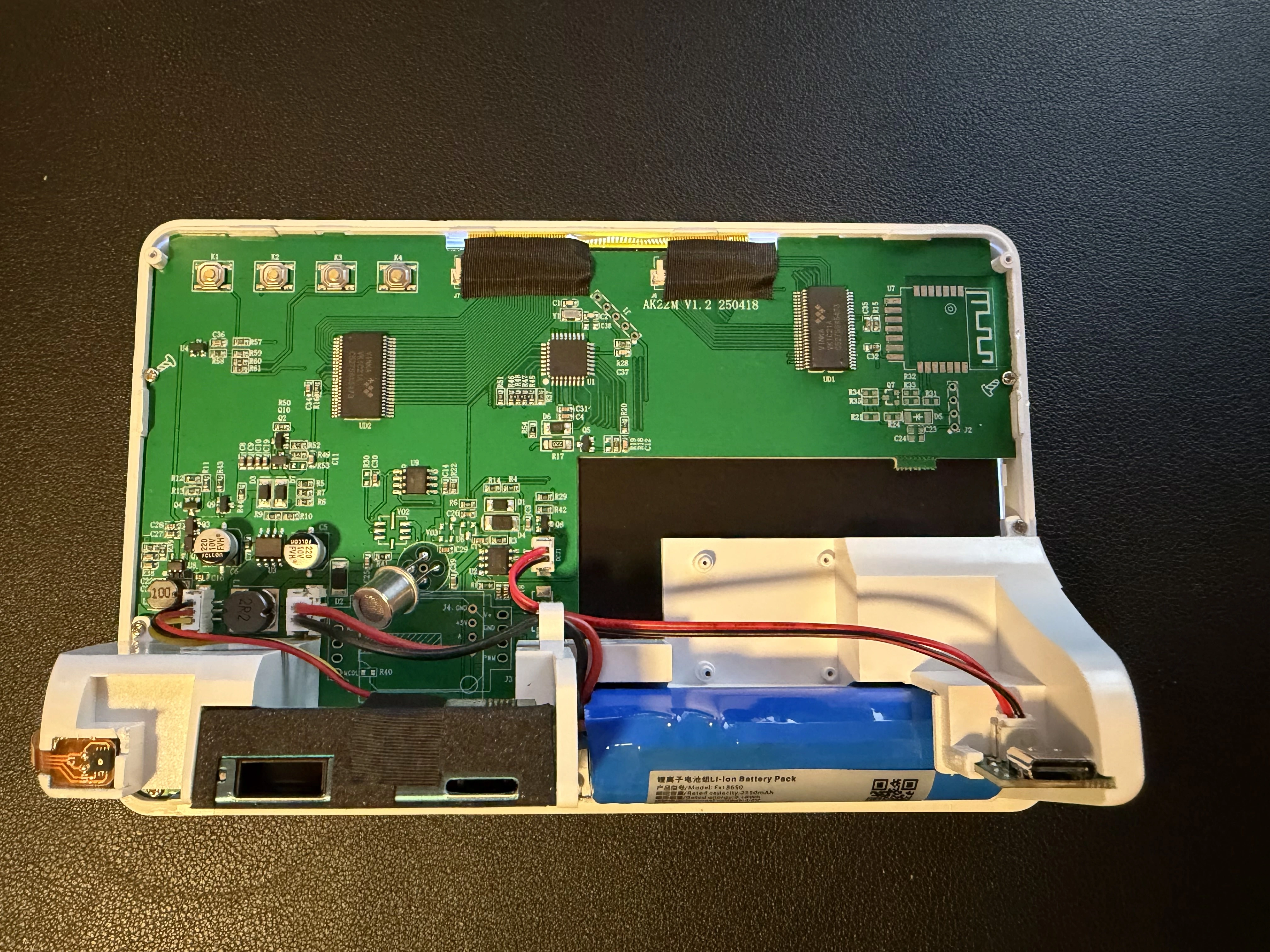
The internal design is fairly typical for low-cost embedded devices: a main microcontroller, a handful of sensor inputs, and a separate particulate sensor module (likely a Plantower unit) connected over a simple interface.
One thing that immediately stands out is that UART is exposed directly on the board:
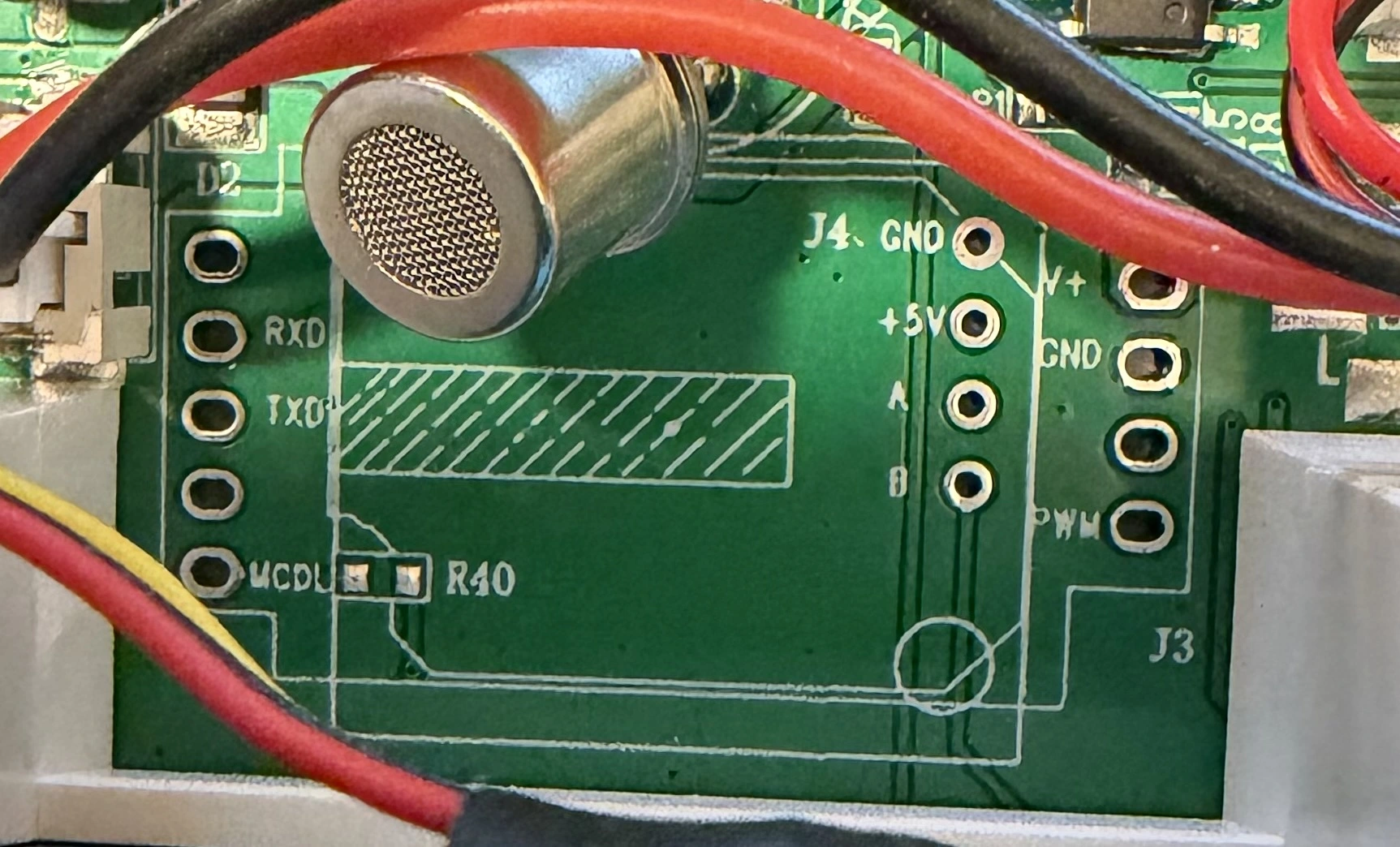
Pins labeled RXD and TXD are accessible, which almost certainly provide a serial interface to the MCU. In many devices like this, that UART is used for:
- Debug logging during development
- Factory programming or testing
- Sensor communication passthrough
With a USB-to-TTL adapter, you could connect directly and observe traffic during boot or normal operation. Depending on the firmware, this might expose debug output or even allow limited interaction.
Another interesting angle is the trust model between components. Seemingly, the particulate sensor communicates with the main MCU over a simple serial protocol, with no authentication or integrity checking. That means a man-in-the-middle (MITM) style attack could theoretically possible: intercept the sensor’s UART lines and inject modified readings. For example, you could force the device to always display “clean air” regardless of actual conditions. Please note that none of this is tested and verified - just speculating.
There are also clearly labeled headers and test pads on the board, which are likely used during manufacturing for programming or diagnostics. These could potentially provide deeper access to the firmware or device behavior with enough reverse engineering.
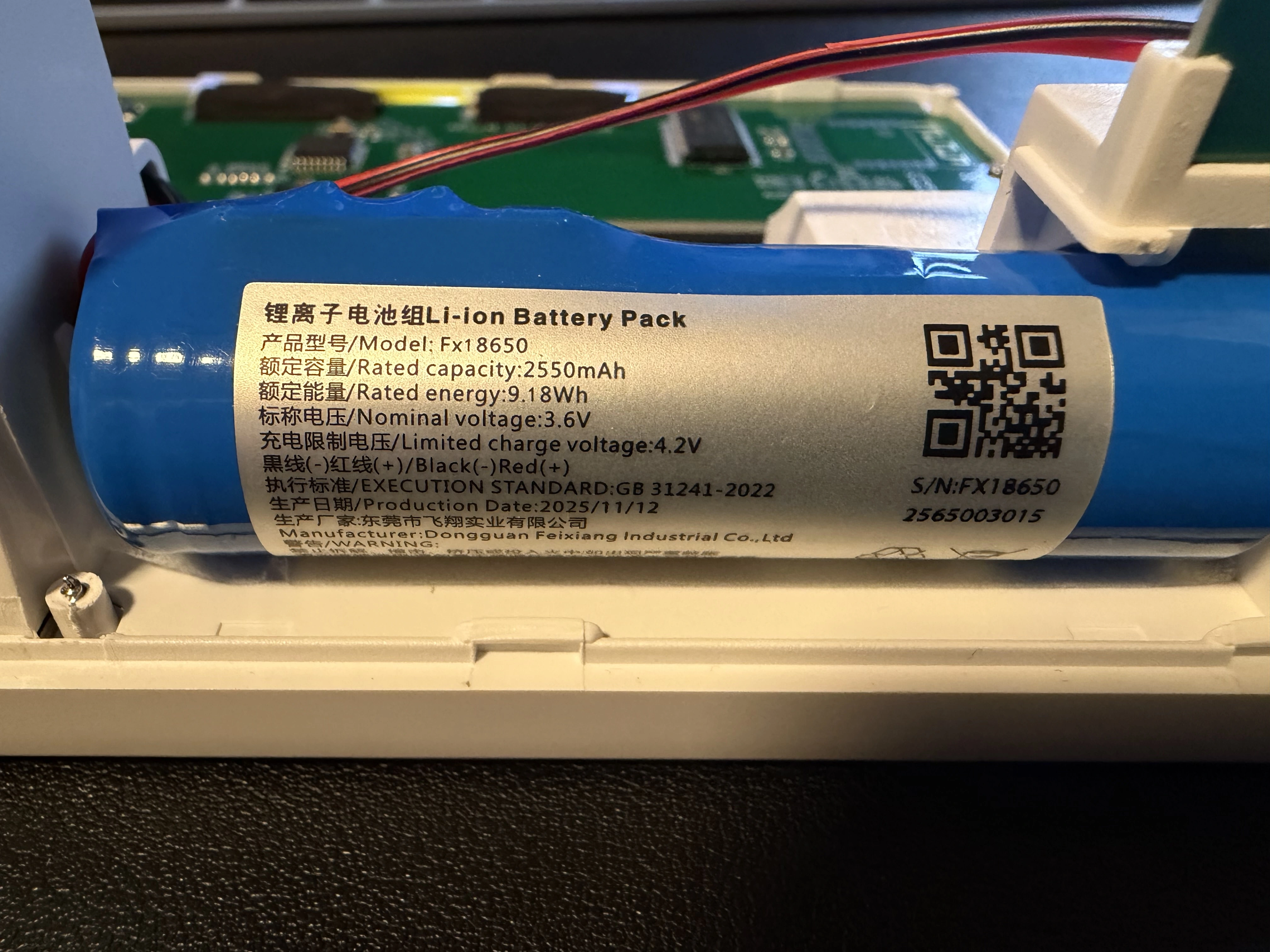
Even at a hardware level, modifications are straightforward. The device is powered by a standard 18650 lithium-ion cell, and there’s nothing preventing you from swapping in a higher-capacity battery to extend runtime. The power circuitry is simple and doesn’t appear to enforce strict constraints beyond nominal voltage.
Overall, while this device isn’t exposed to remote attacks, it’s a good example of how physical access completely changes the security model. With minimal effort and inexpensive tools, you can observe, modify, or potentially control how the device behaves.
Overall
If you’re looking to measure these things at home, this device is a good purchase. For what it is, the screen is high quality. Build strength is good. And if you’re worried about the security of these random IoT devices, the risk here is minimal since it lacks connectivity. Go buy it now.